ABOUT S5T
Built on pedigree. Run with purpose.
Scorpion Five Technologies is a US-based, SDVOSB-certified technology and digital marketing firm. Every engagement is owned by a seasoned expert — not delegated to juniors, not handed off between teams.
Deep Technical Expertise
Advanced capabilities in expert hands
Compliance Mastery
Forged by securing classified systems.
SEASONED EXPERT OWNERSHIP
Matched to your work – owns the results
SDVOSB CERTIFIED
Service-Disabled Veteran-Owned
THE NAME
What inspired the name Scorpion Five?
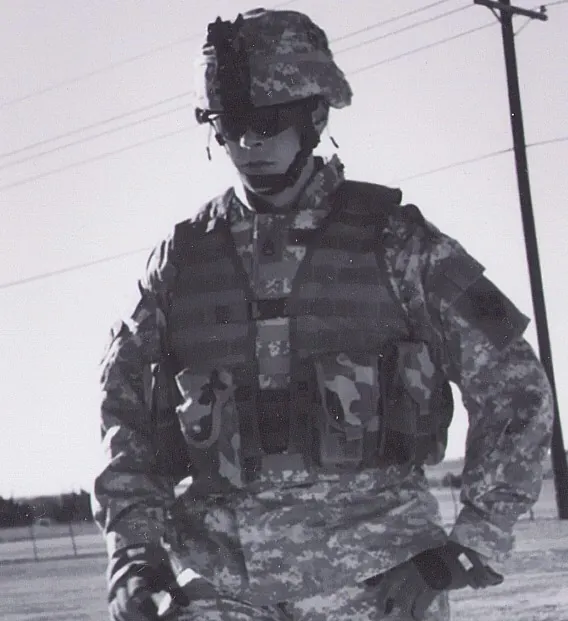
We at Scorpion Five Technologies (S5T) draw not only our name, but also our drive to endeavor for excellence, from fallen US Army Infantryman, SSG. Christopher J. Schornak. As a squad leader in the “Scorpion Platoon,” he went by the radio call sign “Scorpion Five.” One member of his squad was a young private named Eddie “Hildy” Hildebrandt, our founder.
It is from Schornak that we learned to be clever, tenacious, and precise, but also to embrace good old-fashioned American grit! Even more importantly, we learned the importance of aspiring to have world-class expertise and capability, without fail, every single day!
Allow us to show you the difference these convictions make when we build and deliver to you the bespoke software, world-class enterprise systems, and advanced digital marketing you need to build the organization you envision!
THE FOUNDER
The background that built the firm.
Eddie “Hildy” Hildebrandt is the founder and CEO of Scorpion Five Technologies (S5T), and a Tampa, Florida trailer park escapee. His professional journey began in 1996, at age 14, in Gainesville, Florida. There he worked for a company that primarily built agricultural fencing, but also did some roofing and picked watermelons. Later, Hildy made his way into the restaurant industry and earned his first management position at 16.
By 2004, his young and restless ambition had led him to perhaps too many management positions — by this time he was leading a crew of about 60 as a kitchen manager in Brandon, Florida. But even though he held two jobs at times, it was wheel-spinning at best. He decided to make a dramatic move.
Armed with a GED and a sixth-grade education, Hildy joined the mighty US Army Infantry in 2004 and shipped out to Iraq in 2005. The decision to join was the single most impactful decision Hildy ever made in his career. Indeed, the very company he leads today was named after the radio call sign of his fallen squad leader, SSG. Christopher J. Schornak.
Hildy left the Army in late 2007, returned home to Florida, and started a successful construction company with a close friend. He also ran live music promotions during this period and spent a lot of time on stage playing guitar, most notably with the band Ebullition.
In 2012, Hildy sold his half of the construction company to start college and a new business: Hildebrandt Guitars. Hildy had become well-known not only for guitar playing, but also as a luthier. It was during this time that Hildy was introduced to programming — first via modifying the G-Code that ran his CNC machines, and soon after the post-processors in his CAD-CAM programs that calculated toolpaths and produced the G-Code. He also had some light academic training as well via his MIS degree curriculum.
In 2019, Hildy took a software engineering position with a company in North Carolina, where he architected and built large enterprise systems, then successfully accredited them for use on some of the most secure networks on earth — in addition to building and leading multiple development teams comprising the dozens of developers that accomplished the work.
In 2024, Hildy came to the realization that the personal satisfaction he felt as an entrepreneur and business owner was not something he could give up. This drove him to form S5T, which brings us to today. His intent is to create a technology development and digital marketing company that is simply more advanced and elegant than the rest.
CORE VALUES
Clever, tenacious, precise.
Not a values poster. These are the operating principles the firm was built around.
Humility
Be proud of what you’ve accomplished and what you are capable of. But always remember that Hubris blinds you to exploring new opportunities and threats alike.
Tenacity
Having the drive to continue on, even when everything seems poised to stop you, is far more valuable than education, intelligence, and resources.
Cleverness
Be adaptable to situations and conjure solutions that come from angles less imaginative people wouldn’t dare to explore.
Precision
Do not merely hit the bullseye, aim for the center of the bullseye.
Boldness
Be careful not to allow fear to manifest as prudence or strategic thinking. To reduce risk is wise, but to try and eliminate it is fear and weakness working as one.
HOW WE WORK
One expert. One engagement. One outcome.
The PI Model
Your engagement is owned by a named PI from first conversation through delivery. The expert you meet is the expert who does the work — not a sales rep handing off to a junior team.
No hand-offs
There’s no account manager between you and the work. The PI owns the relationship, the strategy, and the output. If something needs to change, you have one conversation with one person.
Matched by situation
S5T matches each client to a PI whose expertise fits the actual problem — not who is available this week. Depth over coverage.
HOW WE OPERATE
Three lines of work. One standard across all of them.
S5T operates across three distinct lines of work — private-sector services, federal contracting, and owned digital products — and the discipline built in each one enhances the others.
Private-sector services. Marketing programs and technology builds for growth-stage businesses and compliance-restricted technical buyers — expert ownership of the functions that directly affect revenue and growth.
Federal contracting. SDVOSB-certified, with defense and intelligence pedigree. Mission-level work for DoD and federal programs — a long-horizon line of work rooted in the experience that gives S5T its technical depth.
Owned digital products. A growing portfolio of businesses S5T builds and operates itself — from eCommerce to SaaS to developer tools. The same problems clients bring to S5T, managed from the inside.
WHO WE SERVE
Work that fits. Nothing else.
S5T works with three kinds of clients. Each is different. Each is underserved by the usual options.
The business that outgrew its tools.
Healthcare practices, legal firms, financial services. You’ve built something real — but the patchwork of tools and vendors you’ve accumulated no longer scales with where you’re trying to go.
The technical buyer who needs the pedigree to be real.
Mid-market and enterprise teams navigating FedRAMP or CMMC requirements. You need a firm whose people have genuine experience in this environment — not one that claims familiarity.
The program that needs mission-level performance.
DoD and federal programs that need contractors who understand the mission environment from the inside. SDVOSB-certified, with key personnel who’ve operated in that environment. The depth is real — it comes from hard-won experience.
CREDENTIALS
SDVOSB Certified
DoD & IC Systems Experience
FedRAMP / CMMC / HIPAA Fluency
Enterprise Systems Accreditation
Full-Stack Digital Marketing
Principal Investigator Delivery Model
WHO WE SERVE
Three kinds of clients.
If you see yourself below, a discovery conversation is worth your time.
THE GROWTH-STAGE OWNER
You built it. Then you outgrew it.
You run a successful small business in a regulated industry— a med spa group, a legal practice, a financial services firm. You’ve outgrown the patchwork of tools and part-time vendors that got you here. Now you want seasoned expertise. Someone that has built real systems and sophisticated marketing plans. Someone who will learn how your business operates and use holistic tech and marketing approaches to support your growth.
THE COMPLIANCE-BOUND TECHNICAL BUYER
The spec is hard. The compliance floor is harder.
You’re a Director, VP, or CTO at a company whose software has to satisfy FedRAMP, CMMC, HIPAA, or some other complex regulation. You’ve been burned by vendors who claimed compliance fluency and couldn’t perform. You want a team whose founders actually shipped advanced accredited systems, and who can walk your auditors through the work and achieve favorable outcomes.
THE MISSION OWNER
Government PMs, directors, and COs.
You’re a program manager, contracting officer, or technical lead inside DoD, the IC, or other heavily compliance-bound agency. You need contractors who deliver on time, own their deliverables, and have a history of building and successfully accrediting advanced software and cloud systems. Our founders have done exactly that. Checkout our capabilities statement to learn more.
Discovery calls are a conversation, not a sales pitch. 30 minutes, no obligation.
